self-management
Make It Easy and Secure
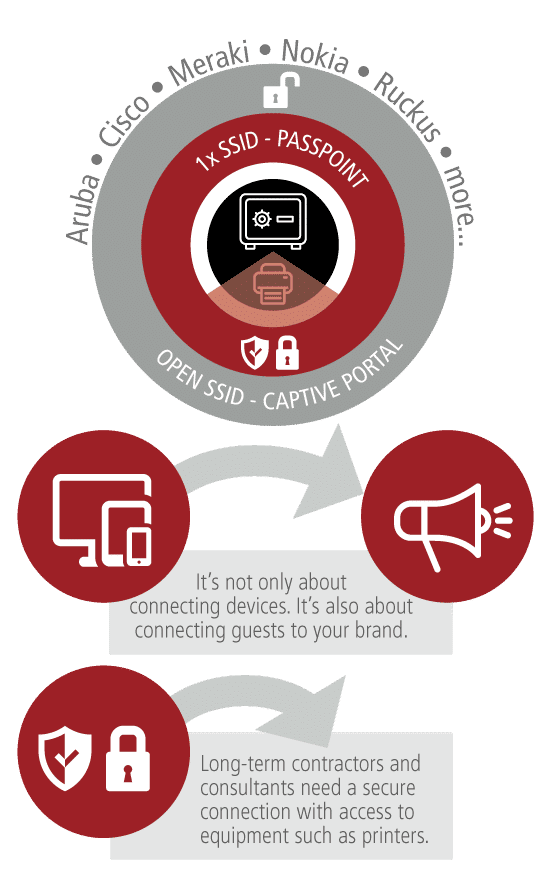
Enterprise Guest Wi-Fi is much more than just providing Internet access to visitors and bring-your-own-device services for employees. It is about delivering a consistent user experience and branding. And allowing non-IT employees to update captive portals and offer secure access to networked resources for long-term contractors.
Enterprise Guest Wi-Fi
User Story – John 34
- Guest Internet services. John is a 34-year management consultant. He is visiting BigCorp’s HQ in London to discuss a significant international project. Arriving early after his flight, he looks for the guest Wi-Fi in the reception. John connects with his smartphone and enters his details and cellular phone number in the captive portal. Ping! John gets a one-time password via SMS, which he also can activate with a simple click on the embedded URL.
- One week later. John is heading to BigCorp’s Tokyo office. John notices a different brand of Wi-Fi equipment hanging from the ceiling. He wonders if there are any guest Internet services. He switches on the Wi-Fi and is amazed at how consistent the guest Wi-Fi portal experience is. As a consultant, he appreciates these things. Brand identity is essential. But, he also likes the local information, including the map, to find his way between the buildings on the corporate campus.
- Back home in Oslo. John gets an e-mail confirming the eight-month project in Tokyo. He is excited. BigCorp asks John to onboard Hotspot 2.0 Passpoint certificates on his devices by clicking on a link sent via SMS and e-mail. Once these certificates are installed, John will get encrypted Wi-Fi and fly on to the secure guest Wi-Fi in Tokyo (802.1x SSID). He will also have access to office equipment such as printers and conference projectors. The portal automatically detects that John is using Windows. After an additional verification through a one-time password sent through SMS, a short video guides John on how to install the certificate.
- On his first day in Tokyo, John’s smartphone is onboarded to the secure Wi-Fi network, although the smartphone does not support Passpoint R2 for online sign-up. How? He benefits from Enea’s pragmatic approach to Passpoint, utilizing Passpoint R1 and the captive portal API (RFC8908 and RFC8910).
If You Can’t Secure the Enterprise Guest Wi-Fi – Trace It
In an ideal world, guests should always connect to a secure guest Internet SSID (Wi-Fi network ID running 802.1x). But we are not quite there yet. You will have to balance security with convenience for your guests. The need for unencrypted, open guest Wi-Fi SSIDs will not go away soon.
The one-time password delivery in an SMS, with a clickable link, was very convenient for John. But it was also crucial for security reasons. If you use an open guest Internet SSID, you must be able to get traceability. This is precisely what SMS verification does. You can tie the guest account and device to the mobile number’s verified identity. And, of course, you must separate the open SSID from your corporate network, e.g., through a virtual LAN (VLAN).
Security for Long-Term Guests
Contractors and consultants should all connect to a secure and encrypted enterprise guest Wi-Fi SSID with 802.1x support. They should be separated from the corporate network but with access to office equipment such as printers and conference projectors.
To connect to this secure Wi-Fi network, you must provision a certificate (EAP-TLS) or username/password (EAP-TTLS) in each device to connect it to the 802.1x SSID. In the future, with widespread device support for Hotspot 2.0 Passpoint R2 online sign-up (OSU), this process will be more automatic. Right now, we have to rely on manually provisioning certificates (EAP-TLS) or username/password (EAP-TTLS) in each device.
Some intelligence supporting users during setup can be built into the Enea Aptilo SMP (Software) or SMP-S (service on AWS) captive portals. If the device supports Hotspot 2.0 Passpoint R1, the user can optionally watch an instruction video on how to install the certificate for that device. The captive portal API (RFC8908 and RFC8910) will help streamline the process.
This will improve the user experience and thus the adoption rate. After the installation, users will get encrypted communications and seamlessly fly onto the secure guest Wi-Fi network.
Access our Wi-Fi Resources Library
You will get access to download all our Wi-Fi-related collaterals including White Papers and Solution Briefs. You may also want to visit our insights section.
If you have any questions, please do not hesitate to contact us!

Get Our Most Wanted Functions
We have collected the most wanted enterprise guest Wi-Fi functions in our cloud service – the Enea Aptilo Guest Wi-Fi Cloud. However, suppose you have special requirements and need advanced integration. In that case, you may choose the Enea Aptilo SMP (software) or SMP-S (service on AWS) with the Enea Aptilo SMP Venue Wi-Fi Manager instead.
Consistency over Multiple
Enterprise Guest Wi-Fi AP Vendors
Deliver a consistent, secure, and reliable enterprise guest Wi-Fi experience across every office in the organization. Vendor-agnostic is not the same as supporting standard protocols. Not in our book. We have added specific adaptations in Enea Aptilo SMP to ensure you get the most out of the hardware from our Wi-Fi partners.
Our enterprise guest Wi-Fi solution, based on SMP, supports all onboarding and login methods. Click & Connect, Micro Survey, Advanced Survey, Account Login, Credit Card payment, Swish (online payment), Office 365 Login, Vouchers, e-Vouchers, SMS one-time password, e-mail validation, sponsor approval (the host for a meeting approve visitors access), Facebook login, LinkedIn login, Twitter login, WIFI4EU login, group accounts, long-term accounts and Certificates (EAP-TLS/TTLS). We can also integrate with your Active Directory (AD) and provide Bring-Your-Own-Device (BYOD) service flows. You name it. We’ve got it!
One Brand Identity – Local Diversity
Global Enterprise Guest Wi-Fi
Captive portals should be a business communication tool. With Enea Aptilo SMP, anyone can make updates to the captive portals. Those pictures and texts defined as editable in the template can easily be changed. Let your local receptionist write a welcome message to an important visitor. Provide local information such as maps of the campus. You can make these changes down to a local office area. And schedule captive portals to kick in at a specific date and time.
Use Wi-Fi analytics to get actionable insights about your visitors. Use our Wi-Fi Marketing to bring information and messages to your visitors,
