White Paper Excerpt
Why Cellular IoT Is Another Story
Hyperscale Cellular IoT – White Paper
This is an excerpt from our white paper Hyperscale Cellular IoT. The full white paper is available here if you like what you read. Don’t hesitate to contact us if you have any questions.

Mobile Operators that think they can create Internet of Things (IoT) connectivity services by re-packaging existing cellular consumer services need to think again. It’s not just a matter of adding IoT SIM management capabilities to an existing mobile core. Enterprise IoT customers need so much more in terms of flexibility and security.
It’s a giant step to go from offering consumer services, with a handful of subscriber-types and associated policies, to providing complex IoT connectivity services. In IoT, each customer has their own unique requirements.
Some IoT customers need all or part of the traffic delivered in Private APN connections (APN + Enterprise VPN). IoT device security is crucial, and customers want to protect the traffic through firewalls. Other customers want to manage their own connectivity and security policies per device / device groups from a web portal. Others need local subscriptions in specific countries, not the least where they prohibit permanent roaming. And they want a unified experience across these international networks. This means that operators are facing challenges to keep settings, such as policies, security and IP-addresses, across partner networks, even when an eSIM has been localized.
“The bottom line is this, customers need a programmable and secure global IoT connectivity service that they can deploy instantly. Mobile operators will realize that they cannot deliver this from a mobile core created for consumer services.”
So, what is then the way forward? How will operators be able to deliver what their IoT customers need?
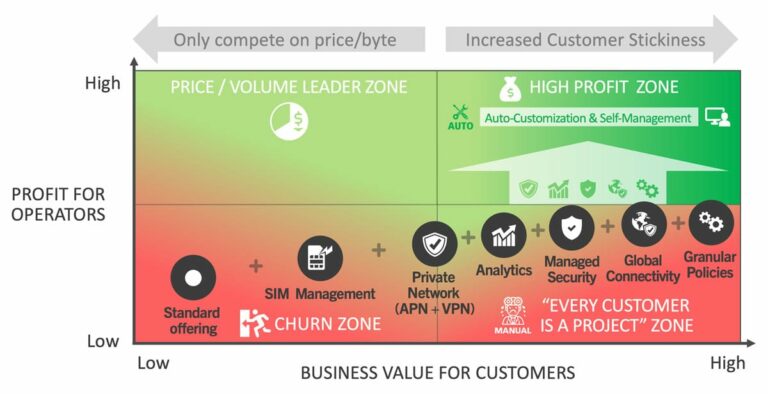
The matrix shows two perspectives that operators need to consider when creating IoT connectivity services. On the X-axis, we have the business value the service brings to the Enterprise IoT customer. On the Y-axis, you find the profit the IoT connectivity service brings to the operator.
Mobile operators will end up in the bottom left corner, if they just re-package an existing consumer standard service for IoT.
Most operators also add SIM-management and offer private connections on top of this. The keyword here is ‘most’. They will deliver a commodity with little value add for their customers. Those operators will only compete on price, and the lowest bidder will replace them. They are in what we call the “churn zone” colored red in the matrix.
In the left half of the matrix, operators will only be able to create a profitable IoT business if they become the price and volume leader in their market.
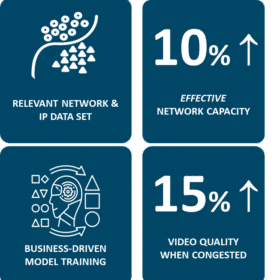
The further you move towards the right, adding value-added services, the stickier customers become. Higher revenues come with value-added services such as analytics, managed security, global connectivity and ability to provide granular policy control.
For most operators, the high profit will not follow when adding value added IoT services. They will be stuck in the bottom right corner, in what we call the “Every customer is a project zone”, with expensive development projects to create what customers need.
In the upper right corner, we have the green high profit zone with a high value for customers combined with high profit for operators. To go there, mobile operators must add as much automation as possible when it comes to customization and also provide customer self-management. This serves two purposes. First, operators will get a lower cost of operation. Second, customers will not be so cost sensitive as the service feels like their own when integrated tightly with their operations.
In IoT There Is Just No Such Thing as One Size Fits All
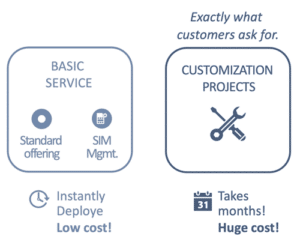
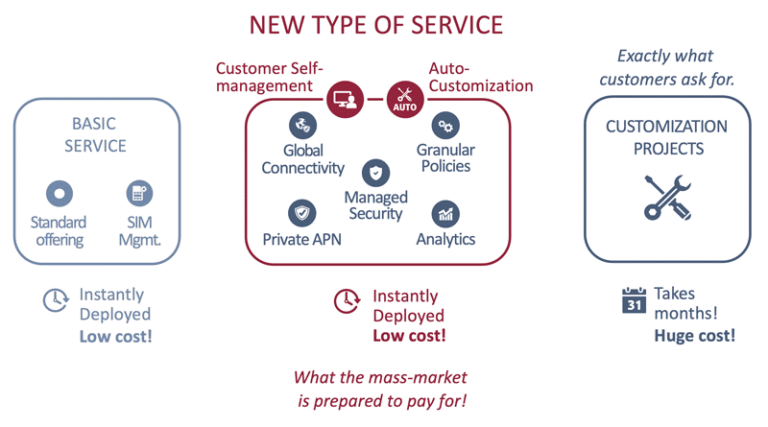
As discussed, most operators offer basic IoT connectivity services. The next step up from that is often a completely customized IoT connectivity service, where each customer deployment becomes a costly project. IoT customers are more demanding when IoT goes from initial proof of concepts to become critical to their operations.
“The bottom line is this, customers need a programmable and secure global IoT connectivity service that they can deploy instantly. Mobile operators will realize that they cannot deliver this from a mobile core created for consumer services.”
This mass-market comprises customers that are prepared to pay for value-added services, but not for tailor-made development in costly projects. A key success factor for this segment is that the mobile operator can automate most of the customization. Another is that customers can tailor the connectivity further to meet their needs from self-service portals.
These services include the capability to set up secure VPN connections, get a managed firewall for increased security, set granular policies, get analytics and being able to localize eSIM internationally. All the features we recognize from the green sector in the matrix on the previous page. This requires a new approach, a new kind of IoT connectivity service.
What Customers Should Expect
Besides their core operations, most enterprises are also in the “trust business”. Thus, the cost of a security breach goes further than the direct impact. There are examples of companies that even have gone bankrupt after a serious incident.
Now, with the rapid growth in IoT, the risks have increased by magnitudes. IoT is a victim of its own success, with the enormous volume of devices. This is putting more pressure than ever on IT departments. Most IoT devices are also headless and thus not handled and monitored by users, making IoT security even more challenging. In addition, some of these devices are not physically protected and can be tempered with.
So, IoT customers should not settle with a basic service just providing IoT connectivity with basic SIM-management. They should challenge their service provider to deliver an IoT connectivity service that fits their needs:
- Rapid deployments with features tailored to create great value just for them.
- Low total cost of ownership over the IoT service life cycle.
- Pro-active IoT security.
- Granular analytics based on IP destination, port & protocol, type of traffic, etc. This is critical for the Enterprise to identify expensive data usage, trouble-shoot and get insights into how devices behave.
- Connectivity protected by a firewall with settings in their own control.
- A private connection (VPN), protecting their traffic from device to back-end services.
- Ability to route selected traffic through the private connection and the rest of the traffic to the open Internet protected by the firewall.
- Decide and control devices’ connectivity and target destinations.
- Filter traffic on protocol / ports and set location- and time-of-day based policies.
- Make use of eSIM and buying access wholesale in remote networks with a unified IoT service experience.
And, yes, you guessed right! There is an Enea offering that enables mobile operators to deliver all the above to meet these demanding expectations from their IoT customers. Learn more about the Enea Aptilo IoT Connectivity Control Service (IoT CCS).