White paper excerpt
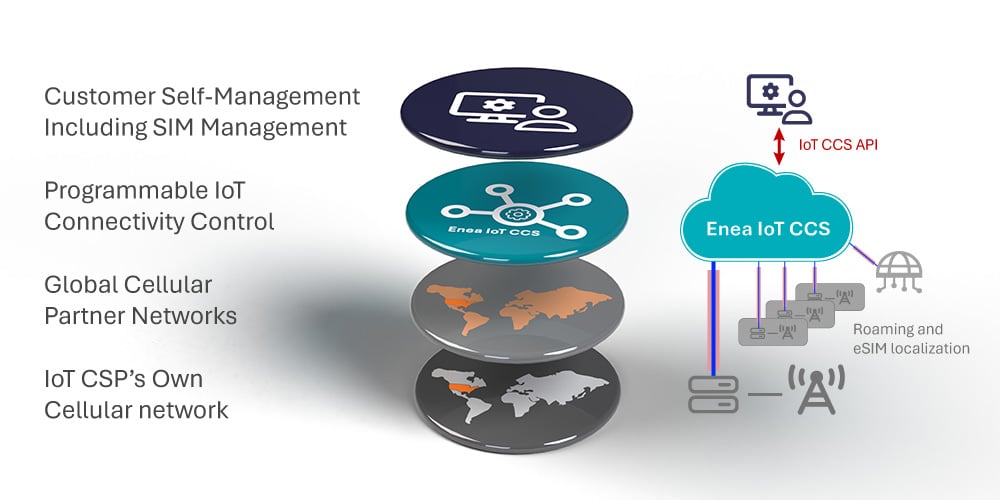
Layers in a Hyperscale IoT Connectivity Solution
Mobile operators must unchain themselves from the strict consideration of 3GPP and mobile core nodes’ implementation and upgrade cycles. The agility they need can be obtained by adding a programmable layer of IoT policy control, security, and automation on top of what they already have.
Hyperscale Cellular IoT – White Paper
This is an excerpt from our white paper Hyperscale Cellular IoT. The full white paper is available here if you like what you read. Don’t hesitate to contact us if you have any questions.

hyperscale solution
The Four Layers
“We have only seen the beginning of hyperscale IoT solutions. The concept of network slicing in 5G is very well suited for this approach. Operators will scale their innovations like never before.”
Let’s examine the four layers in a Hyperscale Cellular IoT solution. In the first layer, we have the mobile operator’s existing cellular network with its mobile core.
The second layer is the global network of MNO partners, either in bilateral agreements or through connectivity hubs. IoT devices can instantly be connected using data roaming. Mobile operators can also localize eSIM/eUICC over the air in countries where permanent roaming is impossible. This means they can offer their customers instant local subscriptions globally in their partner networks.
In the third layer, the mobile operator uses hyper scalers, such as Amazon AWS to deliver a programmable and flexible layer of IoT policy control, security, and automation. All networks, the operator’s own and their partners’, connect to this layer through standard interfaces (Gi/SGi/N6 and REST for the control plane and IPsec for the data/user plane). With this layer in place, mobile operators will keep control even if the device has been localized.
In the last but not least important layer, we find customer self-management portals and the IoT connectivity management platform. Here, the mobile operator can build a web GUI or use APIs and integrate it with the third layer and relevant systems to give their customers complete control over the service. This setup is crucial for the scalability of the mobile operator’s IoT business. The goal is to make the IoT service as much as possible into a “self-playing piano.” The operator’s operations team can also use this to help customers who do not have the skills to use self-management capabilities.
Hyperscale IoT Connectivity as a Service
Mobile operators do not have to build this hyperscale programmable IoT connectivity layer themselves.
There are many advantages to place all the complexity in the cloud, creating a separate programmable layer of policy control, security, and automation. Mobile operators get the freedom to provide optimal and unified IoT offerings with global scalability, something only hyperscalers can provide. With this approach, mobile operators have created something new and groundbreaking – a hyperscale IoT Connectivity service.
But mobile operators do not have to build this hyperscale programmable IoT connectivity layer themselves. Go to our page about Enea Aptilo IoT Connectivity Control Service™ (IoT CCS). Here you can explore more about Aptilo IoT CCS, our pay-as-you-grow service offering to mobile operators.