Full Context Awareness to Protect Against Advanced Exfiltration
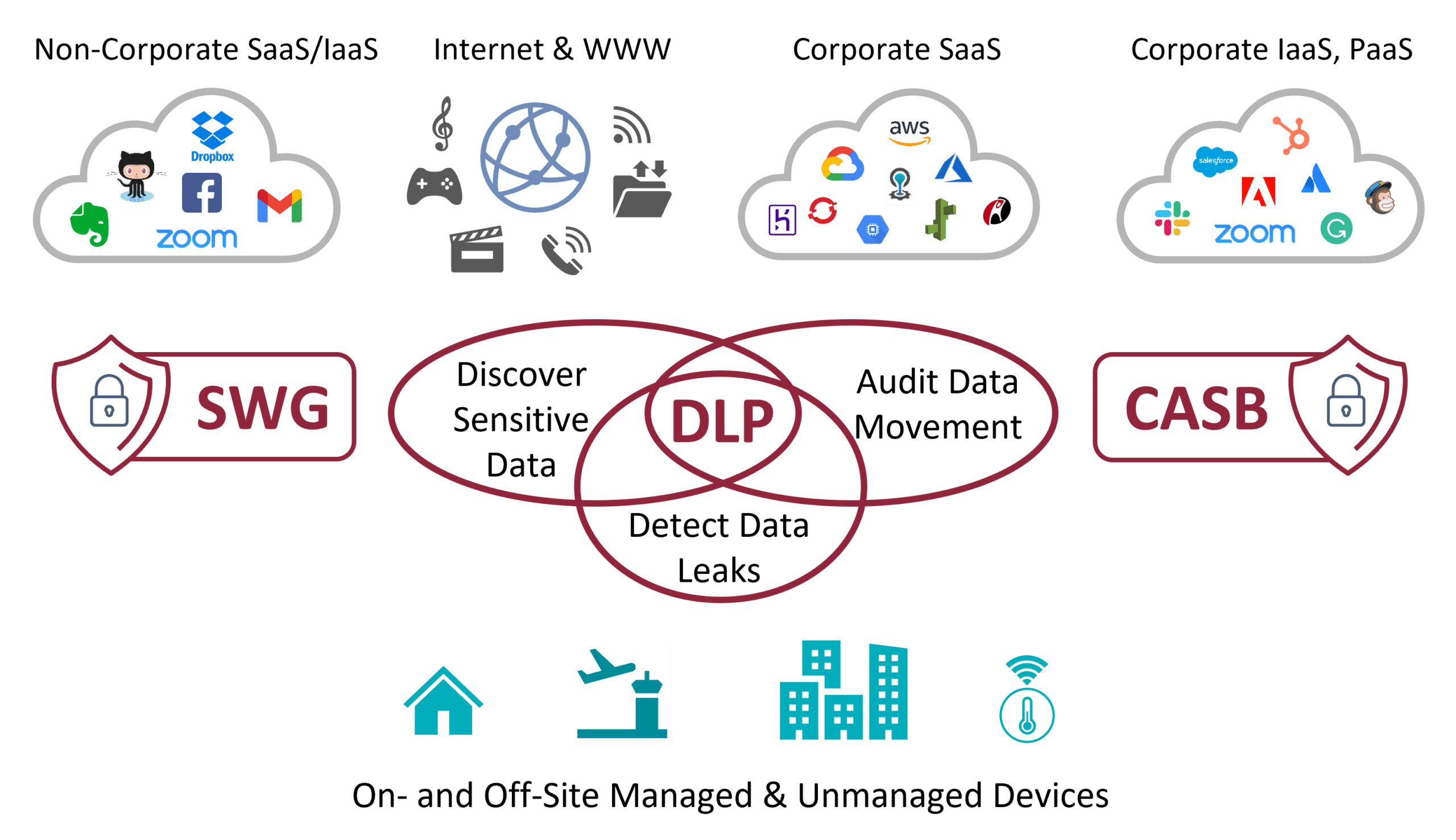
Data Loss Prevention (DLP) is a must-have security function for all organizations. Used to identify and prevent the theft or misuse of sensitive data (e.g., social security numbers, financial information, account credentials…), to inspect content for anomalies and to identify user activities that do not comply with company guidelines or government regulations, it is an essential first line of defense. Its performance, however, depends on the level and quality of the traffic intelligence it receives and therefore on the deep packet inspection (DPI) technology it uses.
Whether your DLP product is deployed as a standalone solution, embedded within security components like SWG, CASB and NG Cloud FWs, or deployed as a central, shared resource in an umbrella solution like Security Service Edge, to ensure success, you need to provide it with reliable, accurate and detailed traffic information.
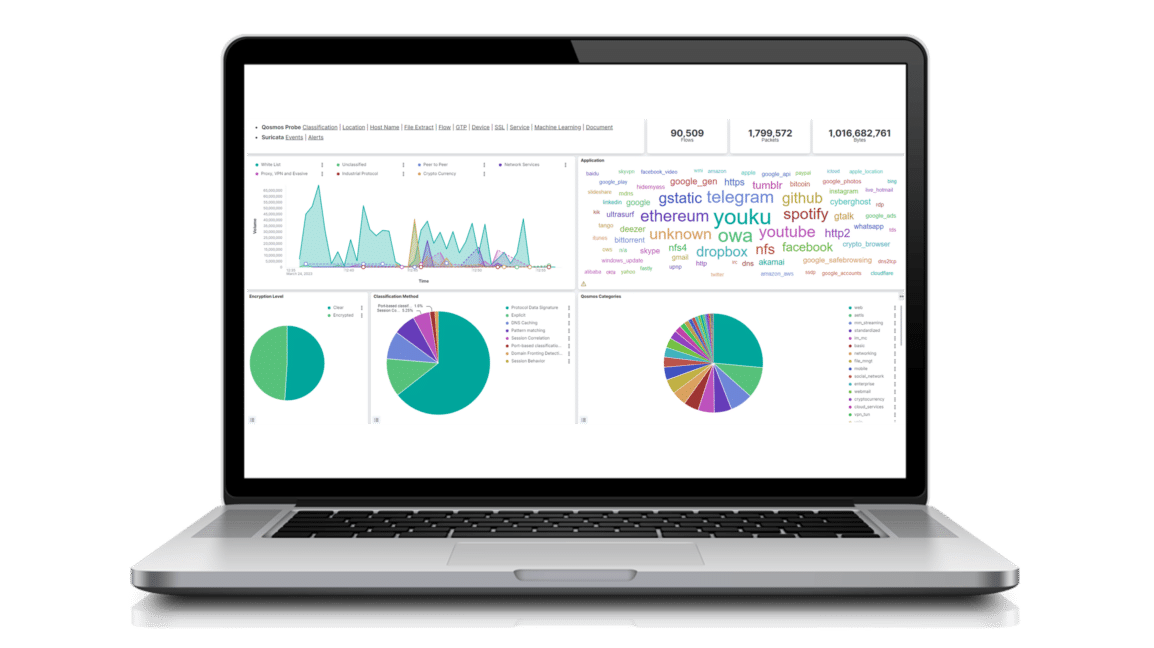
Enea Qosmos ixEngine
Strengthening DLP Solutions with Enea Qosmos Next-Gen DPI Engine
Enea Qosmos ixEngine® is the next-generation Deep Packet Inspection (NG DPI) engine of choice for Tier 1 DLP providers. It provides accurate recognition of 4700 protocols, more than any other DPI engine on the market, and thousands of unique types of metadata that add crucial context-awareness to support DLP functions, including:
- Expanded visibility into user identifiers and actions
- Insights into links and attached files in email
- Extraction of files and/or file metadata (e.g., file extension, size, type, name, content)
- Access to security metadata that enables the identification of tunneling on protocols like DNS or ICMP
- Classification of encrypted and evasive traffic
The Role of Enea Qosmos NG DPI Technology in DLP
Examples of DLP Functions Enabled by Enea Qosmos ixEngine
- Use file hashing to detect a subtle discrepancy between a classified, internal use-only file and a file sent out of the organization via email.
- Extract and inspect an emailed file and sender and device data.
- Identify a data loss source and gather the contextual evidence required for incident investigation and remediation.
- Use L7 classification and metadata extraction to rebuild only objects that are relevant for further analysis, e.g., rebuild HTTP objects when the flow is a targeted blog, not YouTube.
Benefits of Next-Gen DPI for DLP Solutions
- Detect advanced exfiltration techniques like MITM, file spoofing, and tunneling over standard protocols.
- Enhance rules and monitor usage with application-specific user action metadata (in proxy mode).
- Reduce forensic storage by up to 150x compared to full packet capture.
DATASHEET
Enea Qosmos ixEngine: Next-Generation DPI Engine for Maximum Traffic Visibility