High Quality Data and Unique Insights for Superior Anomaly Detection
With increasingly distributed networks, many organizations have adopted Zero Trust Network Access (ZTNA) solutions to strengthen security and reduce their attack surface. This is an important step forward, but a zero-trust posture still cannot provide 100% protection against advanced threats, especially those developed by nation-state actors and sophisticated criminal rings.
For these types of advanced threats, many enterprises are complementing ZTNA and other security solutions with Extended Threat Detection and Response (XDR) systems. XDR systems use behavioral analytics to detect anomalous patterns indicative of an advanced attack. This behavioral analysis is performed on large volumes of enterprise-wide user, device and network traffic data, with rules for actions to be taken to mitigate potential attacks.
The results of this analysis and the effectiveness of the XDR system depend on the information that is made available to it. The more accurate and precise the data fed to the XDR system, the more reliable and successful the detection of the threats.
ENEA QOSMOS DPI TECHNOLOGY
The Data Foundation for XDR
- Identifies 4500+ protocols and applications
- Delivers 5900+ types of metadata
- Classifies encrypted and evasive traffic
- Indicates anomalous behaviors

Enea Qosmos Next-Gen DPI for XDR
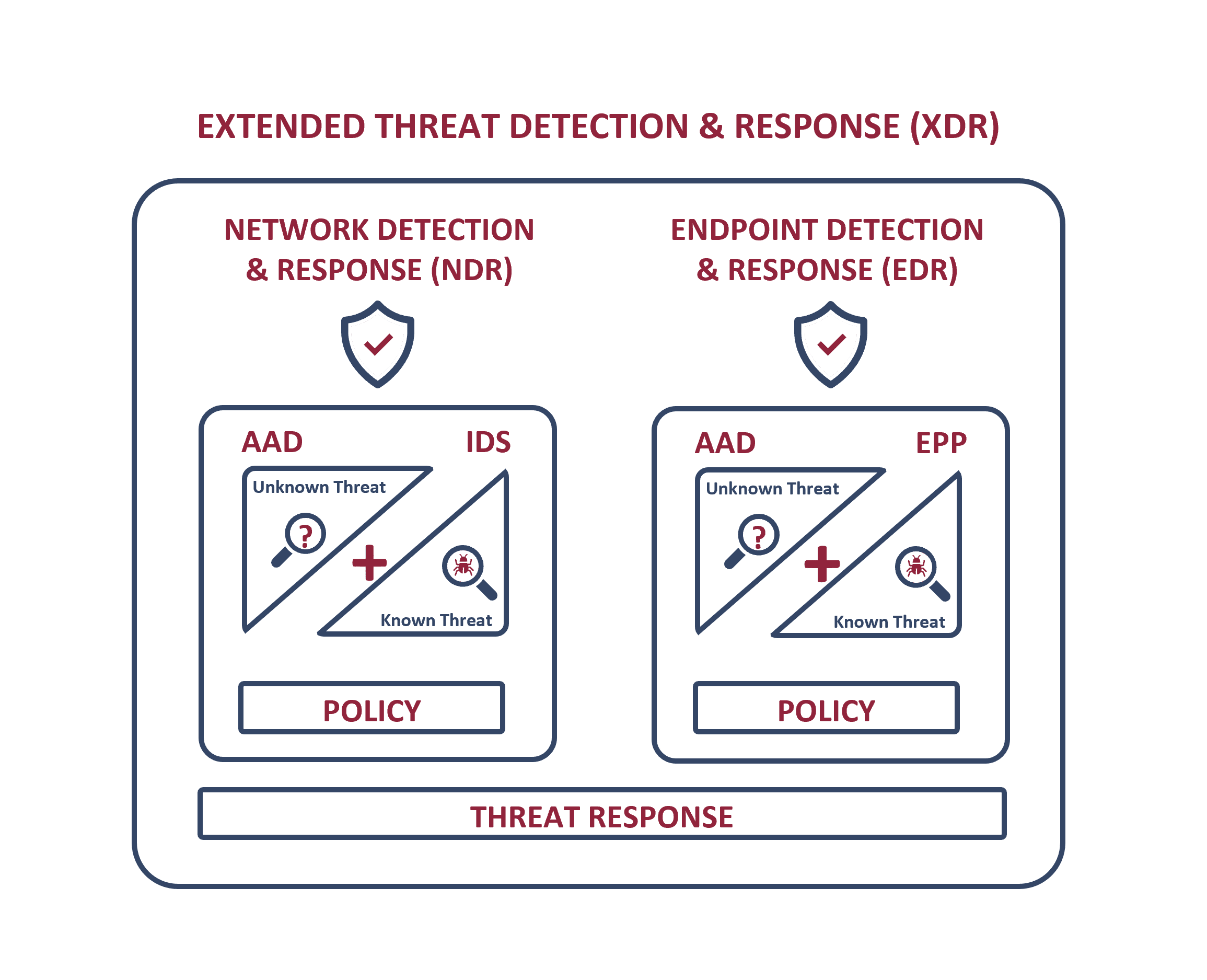
XDR comprises two main functions: Network Detection & Response (NDR) and Endpoint Detection & Response (EDR). As the names suggest, the main role of NDR is to detect and prevent intrusion of the network as a whole, while the goal of EDR is to stop intrusion at the endpoint (e.g., through anti-virus solutions).
Both NDR and EDR use a combination of trusted technologies: 1. Intrusion Detection/Intrusion Prevention Systems (IDS/IPS) for NDR and 2. Endpoint Protection (EPP) for EDR to detect primarily known threats, and 3. Machine-learning enhanced behavioral analyses based on Advanced Anomaly Detection (AAD) to identify unknown or hidden threats that have evaded these systems.
Enea Qosmos technology not only identifies and classifies network traffic, but also provides highly detailed and accurate information on each flow. It is used as a data foundation to support AAD in both NDR and EDR, and to enhance existing rule-based detection capabilities within IDS and EPP components.
Granular Insights for XDR Solutions with Next-Gen DPI Engine
Benefits
Enea Qosmos ixEngine for XDR
Global Network Visibility
-
- Gain real-time L2-to-L7 visibility over network traffic across mobile, cloud, on-premise equipment, IoT devices, applications and containers.
- Achieve visibility into encrypted traffic with fine grained and contextualized metadata and statistics that can profile and classify data packets without decryption.
Critical Efficiency
- Save valuable SOC staff time (and frustration) by excluding low- or no-value data and better qualifying and funneling alerts.
- Dramatically reduce data storage requirements by excluding safe traffic and reducing the need for full packet capture to support forensics.
Maximum Agility
- Rapidly deploy (or re-deploy) sensors as needed across continuously evolving network environments.
- Leverage protocols, metadata, behavioral baselining and analytics to surface new, hard-to-detect threats moving laterally across your network.
- Gain the speed and flexibility needed to secure and manage forthcoming 5G mobile networks.
APPLICATION DATASHEET
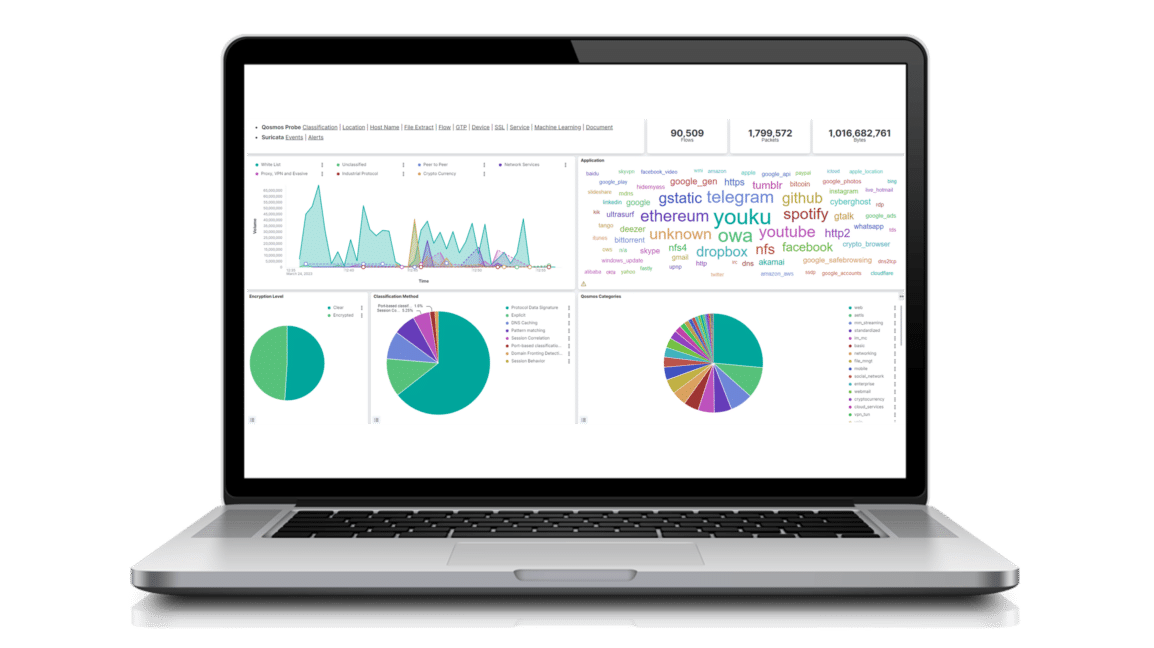
Enea Qosmos Probe for Advanced Network Detection and Response Solutions
“Modern cybersecurity models such as zero-trust networking access and extended detection response pivot around DPI, a trusted technology we all know, but one that’s evolved to meet the needs of the threat landscape today. A strong DPI engine is central to high-performance threat detection. Not only does it enable visibility into network traffic, but it also provides the intelligence around which to base custom rules that customers can tailor to their specific environments.”
Roy Chua, Founder and Principal, AvidThinkIndustry Recognition



DATASHEET
Enea Qosmos ixEngine: Next-Generation DPI Engine for Maximum Traffic Visibility