Tracking the Trackers: Advanced Rogue Systems Exploiting the SS7 Network
We’re releasing more information this week from our research into SS7 attacks that we have detected live in mobile operator networks over the last year. As covered before, these are misuses of the SS7 network for various aims, including tracking, information gathering, communications interception, fraud and so on. Our previous research has shown that this activity is impacting every region of the world. In this blog I’m going to give some information on what are some of the most complex – and potentially the most interesting – types of SS7 attacker, those we define as advanced location tracking platforms. Their functions and operation have never been publically made known before, and are of a generation beyond those which were raised when the security of SS7 networks was first publically discussed.
This information is from our work with mobile operators around the world who are concerned about their subscriber’s privacy and the security of their network. From our analysis SS7 Location attack techniques range from large numbers of relatively simple attacks, which can be blocked relatively easily, to much smaller numbers of quite complex attacks which are much more difficult to block. It is the sources of these complex, hard to stop attacks that are of most interest today, that is because they indicate a high degree of technical proficiency and – as we will show – must have had sizable investment in them to bring them to the level they are at today. The best way to show this sophistication level, is to give examples of 4 of the most active and sophisticated tracking platforms we have encountered to date. Their names below are designations that AdaptiveMobile use internally, but each are entities that are tracking people around the world today.
Examples of Advanced SS7 Tracking Platforms
SS7-Surveillance//WODEN
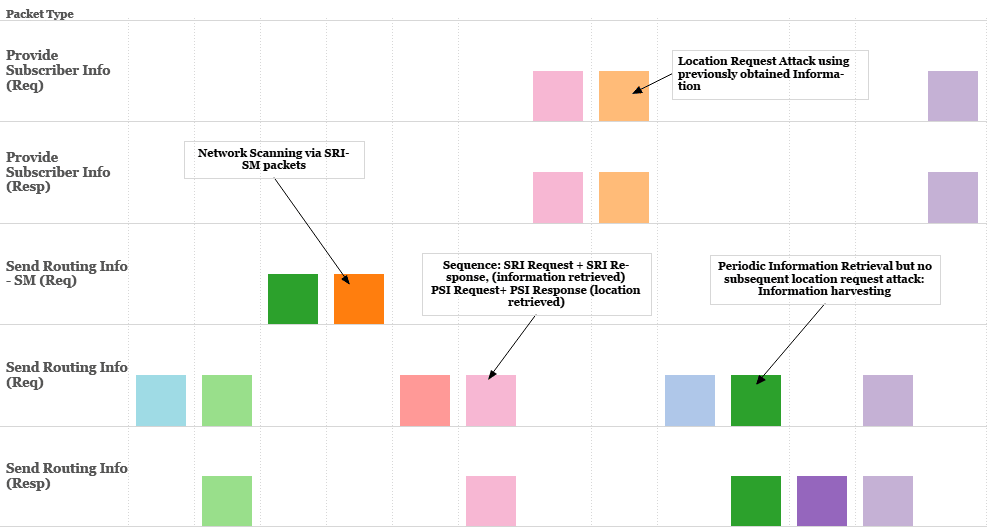
This system’s main technique is to use a combination of first sending a SS7 packet called SRI (Send Routing Information) commands to the tracked subscriber’s mobile network to first get information on a subscriber, and then uses a follow-up command called PSI (Provide Subscriber Information) to retrieve the Cell-ID (location) of a subscriber. This method of ‘staggering’ commands, to gain enough information to allow location tracking matches research which has been previously presented on techniques in this area, however in real-life the attacks are more complex as some information harvesting fails, but also multiple queries are on-going. As well as that we see evidence that the platform itself scans the target networks constantly using SRI-SM (Send Routing Information for SM), looking to improve its information of their network. The following is a time series diagram that shows this activity over several hours, with the different colours representing different subscribers being tracked:
Its complexity and interest to us is both the packet combination it uses, and the fact that its origin points are registered to all of the major mobile operators in a Western Europe country. To explain, that means that the tracking platform is registered with SS7 SCCP layer Global Titles (the rough equivalent of IP addresses in SS7 networks) that assigned to the different operators in that country. However this does not mean that the operators themselves are directly responsible for the platforms. The platform does exist in this country, but the addresses assigned to it may not be under the control of the operators in question. As for its activity, this platform tracks subscribers from other countries around the world, but seems particularly active sending requests to the Middle-East.
SS7-Surveillance//ASMAN
This system is one of two distributed global decentralised systems that we will discuss. What that means is that like WODEN, ASMAN has multiple source addresses from which it launches tracking attacks. Where it differs is that these are not source SS7 addresses in the same country, but source SS7 addresses in multiple countries – all working in unison to track mobile phone subscribers. This indicates access to a specialist, decentralised global network. Its ‘primary’ address from which it launches tracking is based in the Middle-East, but it has backup platforms in Africa, Europe & Asia.
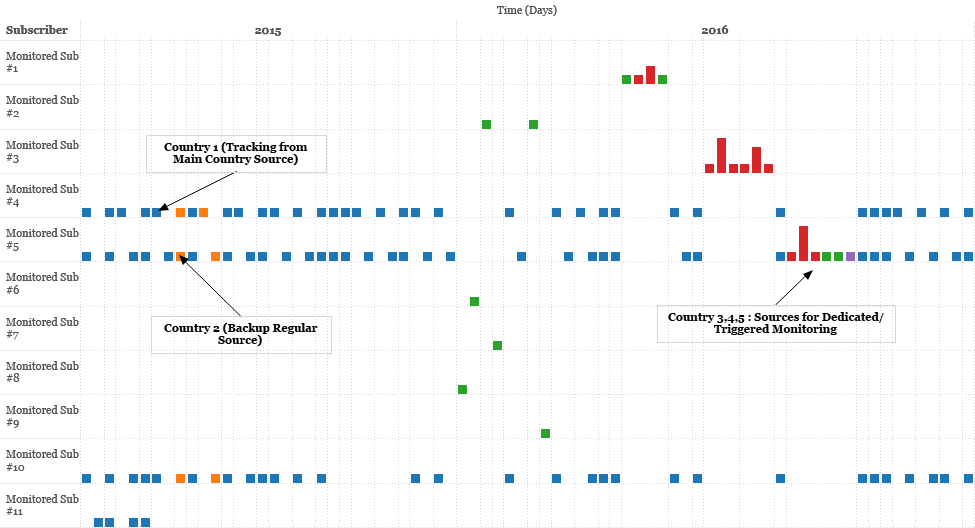
The system itself is quite similar to the others, using PSI packets to track subscribers, along with other SS7 operations to scan and generate information needed beforehand. One hallmark of this system is that victims can be tracked via a variety of means, it seems from the network behaviour we have observed that they can be set up to be tracked once a day, with a very regular time period, or else tracked more intensively, by either involving another set of periodic daily request from a different address, or a dedicated sequence of lookups.
Above you can see a variety of subscribers being tracked over many days in 2015 and 2016. It is clearly evident that some subscribers are attempting to be tracked everyday, while others only receive occassional attention.
SS7-Surveillance//MANNAN
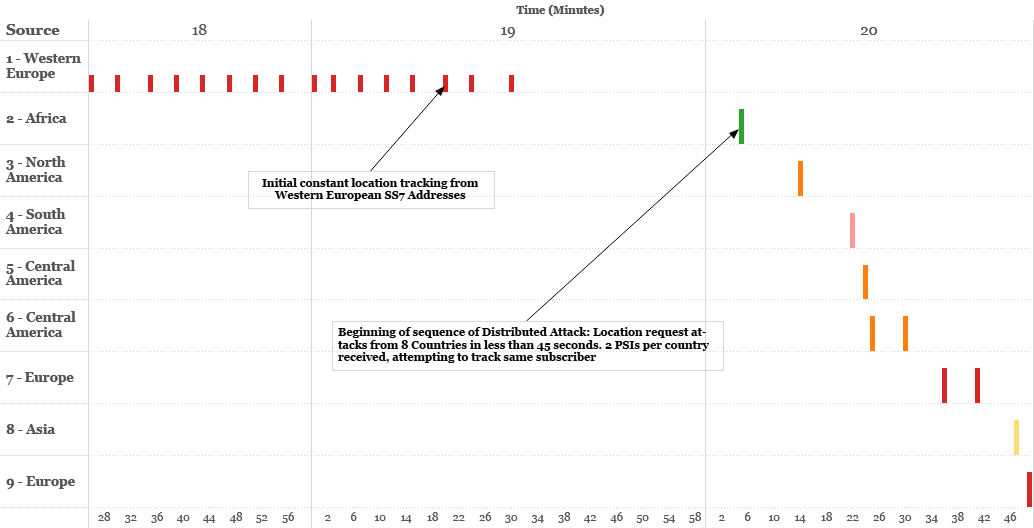
This platform – MANNAN – is a global system, like ASMAN, with multiple origin points to choose from. Its scale however is much bigger – it has access to the SS7 network from sites in nearly every continent in the world. It is also remarkable for its co-ordination, over less than one 3 minute period we tracked a co-ordinated tracking attack using PSI packets from multiple countries, attempting to locate mobile subscribers.
This co-ordination marks MANNAN out as being incredibly complex, as the means to setup, maintain and control multiple SS7 network elements to act simultaneously in different parts of the world requires significant investment and constant work. Its ‘host’ telecom network operators tend to be based in smaller countries where access may be easier to obtain, and the wide world-wide spread ensures that any subscriber of interest in a target country can be queried from multiple points, until one of them succeeds. So far this is the biggest and most complex location tracking system we have detected, but not the most active, being only infrequently called upon.
In this time series graph of one subscriber, we can see an interest period in which the subscriber is attempted to be tracked from a source in Western Europe, before a ‘cascading’ sequence of attacks come from multiple continents.
SS7-Surveillance//HURACAN
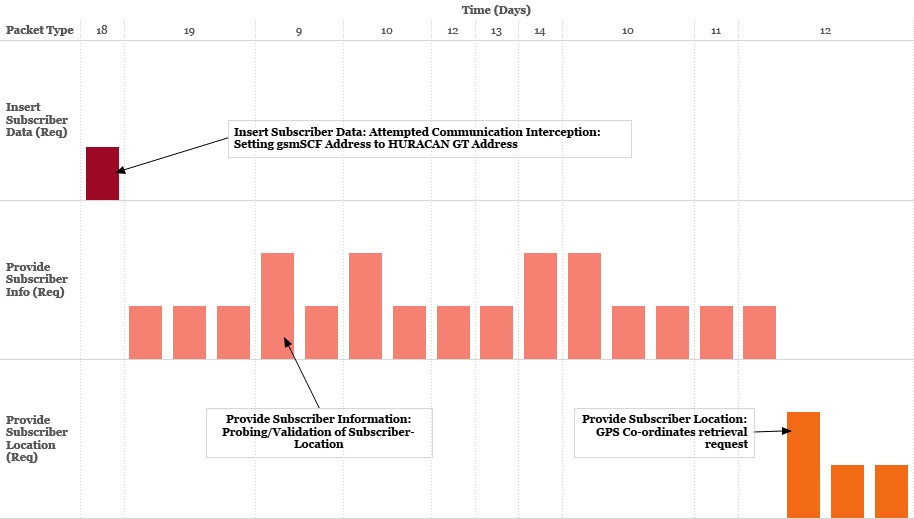
The final platform covered, this system, based in a country in the Americas, is notable for its wide range of attacks and sheer volume of attacks while active. Not only does it execute sophisticated location tracking via PSI and PSL (Provide Subscriber Location) commands, it also does a variety of other types of attacks including interception of subscriber communications via packets called ISD (Insert Subscriber Data), a type of attack theorized but not widely detected in real life until now.
This command instructs the subscriber in question to make a ‘call out’ to a specific network element when communication starts from the subscriber, allows communications interception to happen. Interestingly the order of attacks from this platform varies, in the below example we first detected an ISD interception request being attempted, before multiple PSIs were sent in order to retrieve the Cell-ID & before a PSL command to get more precise location again (GPS co-ordinates can be returned by this method). We have tracked the HURACAN platform sends attacks in large bursts to multiple target operators around the world, especially in the Americas and in the Middle-East.
The above shows the HURACAN platform, over a number of days, attempt to both track and intercept communications from a subscriber. This subscriber was just one of several dozen that this platform was trying to track in the target country over this time period.
Analysis / Quo Vadis
From our analysis, it is clear that this industry has been active for many years, many of these systems behaviours and interactions with the SS7 network are not straightforward and indicate first-hand experience of accessing their target operators over a long period. There are also signs that the platforms are continuing to evolve, to avoid being detected or to improve their efficiency. It is also highly probable that the public research in this area has forced the platform suppliers to try new methods to avoid any attempts to put in place basic protections.
One thing to realise is that these platforms are not tracking the ‘average’ mobile phone user. Instead their function seems to be to perform surveillance on specific, presumably high-profile or high-interest mobile phone users around the world. From our experience the country where you live is also a factor, if you live in a country or in a region that is experiencing geopolitical instability then there is higher frequencies of external surveillance via SS7 means. However countries in more ‘stable’ regions also show incidents of tracking.
Another thing to realise, is that while these tracking platforms may be assigned SS7 addresses within the number range assigned to mobile operators in a country, it cannot be said that these mobile operators are directly involved. In many cases mobile operators may simply be the unwilling host for these systems on their network, or not even be aware these systems are using addresses assigned to them. This was the information stated in the Russian/Ukraine SS7 incidents from 2014, where multiple people in Ukraine were tracked from Russia via SS7 surveillance techniques. During this incident MTS Russia reported that the address was not under their control, despite it being nominally assigned to them. While it may not be the case for all types of SS7 attacks, the source operators from which these location attacks are launched from, may be just as much a victim as the target operators whose subscribers receive these location attacks.
Finally there is the question of the tracking platform’s ultimate origins and users. On this point we simply have to make some assumptions. While criminal uses via hacked SS7 systems are possible, the scale and focused nature of the system would argue against this. This leads us to the conclusion that the systems have been built and installed deliberately in order to track people around the world, and therefore serve the same espionage functions as the systems used in the Russian/Ukraine SS7 incidents from 2014. We have no direct evidence to prove this, but the scale, complexity, tactics, resemblance to known systems of this nature and the source and destinations all indicate a global focused surveillance effort that has been on-going for some time. And these examples are just some of the most complex, there are several dozen other tracking platforms of varying sophistication that we have encountered, and many more may be active.
What is more certain though, is that it is possible to defend SS7 networks. With our customers and our industry partners in the GSMA we have been leading efforts in this area to define the threats and standardize defences against these types of attacks. These efforts will only continue and strengthen as more information about these attackers and their techniques are discovered and shared.