A New Signature-Based Approach to Detect Rapidly Evolving Malware Patterns
Signature-based intrusion detection and prevention
Intrusion detection and prevention systems (IDS/IPS) are designed to monitor and protect networks from malicious activities. They leverage pattern matching to identify threats by comparing network traffic against a set of known attack signatures. When a match is detected, the system can trigger alerts or take predefined actions, such as blocking the traffic, to prevent the attack.
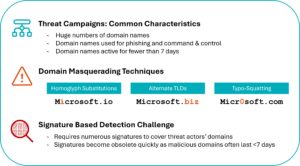
Tactics to Evade Malware Detection
Unfortunately, malware campaigns increasingly evade IDS/IPS detection by rapidly shifting communication patterns, such as domain masquerading (using subtle variations in a trusted domain name to trick users into visiting a malicious website), or the use of short-lived ‘disposable’ websites for phishing campaigns. Such tactics create challenges for traditional signature-based IDS/IPS, which use very large and frequently updated rulesets to keep pace with such rapidly changing attacks. While machine learning approaches can bring high-accuracy to this challenge, they are excessively resource-intensive for systems such as IDS/IPS.
Using Approximate String Matching to Identify Mutating Malware Patterns
To overcome these detection challenges, Enea conducted research focused on a signature-based approach leveraging approximate string matching to identify traffic similar to known malicious patterns—without constant signature updates.
This approach was successfully prototyped in Suricata through the introduction of a new keyword for managing approximate matches without having to create or update rules for every subtle malware variation. It is a strategy that delivers strong detection capabilities with minimal central processing unit (CPU) overhead and significantly outperforms complex regex-based rules. The outcome is a practical, scalable approach that enhances IDS/IPS efficiency against evolving threats.
Pioneering the Detection of Increasingly Dynamic and Complex Threats
The results of this innovative research were presented recently at SuriCon 2025, the annual technology conference dedicated to the Suricata project, organized by the Open Information Security Foundation (OISF).
This research lays the groundwork for adaptive detection strategies and creates new opportunities for threat analysts and rule writers. It enables the development of more resilient and generalized signatures that extend detection coverage, simplify operational maintenance, and accelerate response to emerging threats. It also represents a step toward new IDS architectures that integrate performance efficiency with adaptability, ensuring robust detection in increasingly dynamic and complex threat landscapes.