How to Spot Scam Text Messages And Spam Calls? (PPS Fraud & more)
If you are contacted by someone you don’t recognise, and they ask for personal details or financial information – this could be a scam text message.
Be cautious if confirming any personal information including your email address, phone number, date of birth, or information on anyone in your family. Also, think carefully before clicking on web links or replying to a message either through a call or text message.
What to do if you received a call or text message that looks suspicious?
If you receive a suspicious call or a text message, don’t panic! Breathe and follow the following steps:
- Pause
- Challenge
- Safeguard
First: Pause and think
Don’t be pressured.
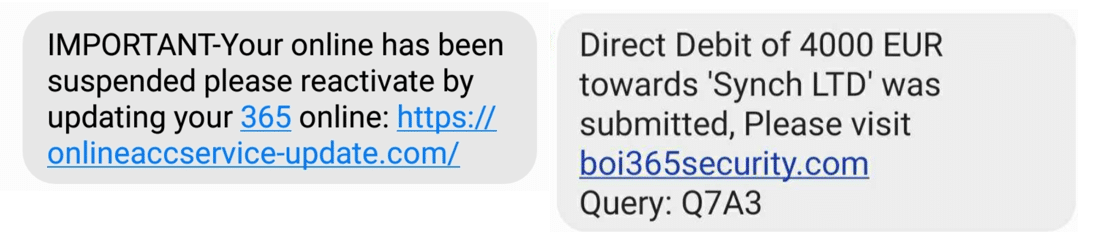
- Fake text messages with web links: Don’t immediately click on a link, no matter how urgent it says the message is. Attackers like to use urgency as a strategy to lure you into their nets.
- If someone has called you, or if you’ve dialed a number you’ve been given in a message, don’t be pressured in to answering questions if you are not comfortable – think about if it is reasonable for that source to be asking for that information. It’s fine to refuse to answer requests, especially if they are pressuring you.
One example of scam calls to be aware of is the one recently reported in Ireland where an automated message informs the recipient that their PPS number has been compromised and requests them to Press 1 to speak with an investigator or official. The caller is then asked to provide personal data.”
*Don’t ever share your personal data such as your PPS number, passport or bank details with anyone.
- If you have a missed call from a number you don’t recognise, don’t immediately call back
Second: Challenge (or test)
If it’s a phone call – Ask the caller to identify whom they are calling from in a way that you can check.
For example, ask them for a number that you can call back on, that you can verify on a website you feel you can trust.
If it’s a message – check the number in your favourite search engine. If it is legitimate, it should be listed on the website of the company or source that you trust.
You can also use the Google Safe Browsing Site checker tool, to verify if the site is unsafe.
Note that with current teleworking, that businesses aren’t always calling from a number you may recognise. However, all businesses should be aware of what programmes they’re running and what their fraud processes are. If in any doubt, hang up or don’t reply and call back on a number that you trust. They should be able to put you through to the right person.
Lastly: Safeguard
If you have provided any information or details and now believe they could be a scam – contact your bank and credit card company immediately, and let them know what has happened. Also report it to your appropriate fraud authority, for example www.actionfraud.police.uk
If you are especially worried, you can also contact organisations that provide services to reduce risk of fraud.
For example, in the UK there is CIFAS.org.uk who for a small fee can provide a protective registration service. These services should mean extra checks are done should anyone apply for a loan using your personal details – to verify it’s you, and not a fraudster. Similar services are available in North America and across Europe. This gives you additional peace of mind.
Think before you click / respond
Always remember that attackers will try to create a sense of urgency in you so that you react without thinking. For that reason, it is very important that you keep control, question any text messages or calls you receive, and if in doubt, go directly to the source of the message to verify the veracity of the message.