Simjacker Vulnerability
AdaptiveMobile Security uncovered new and previously undetected Simjacker vulnerability exploited by surveillance companies for espionage operation.
A New Level of Threat Complexity
The Simjacker vulnerability is currently being actively exploited by a specific private company that works with governments to monitor individuals. Simjacker and its associated exploits is a huge jump in complexity and sophistication compared to attacks previously seen over mobile core networks.

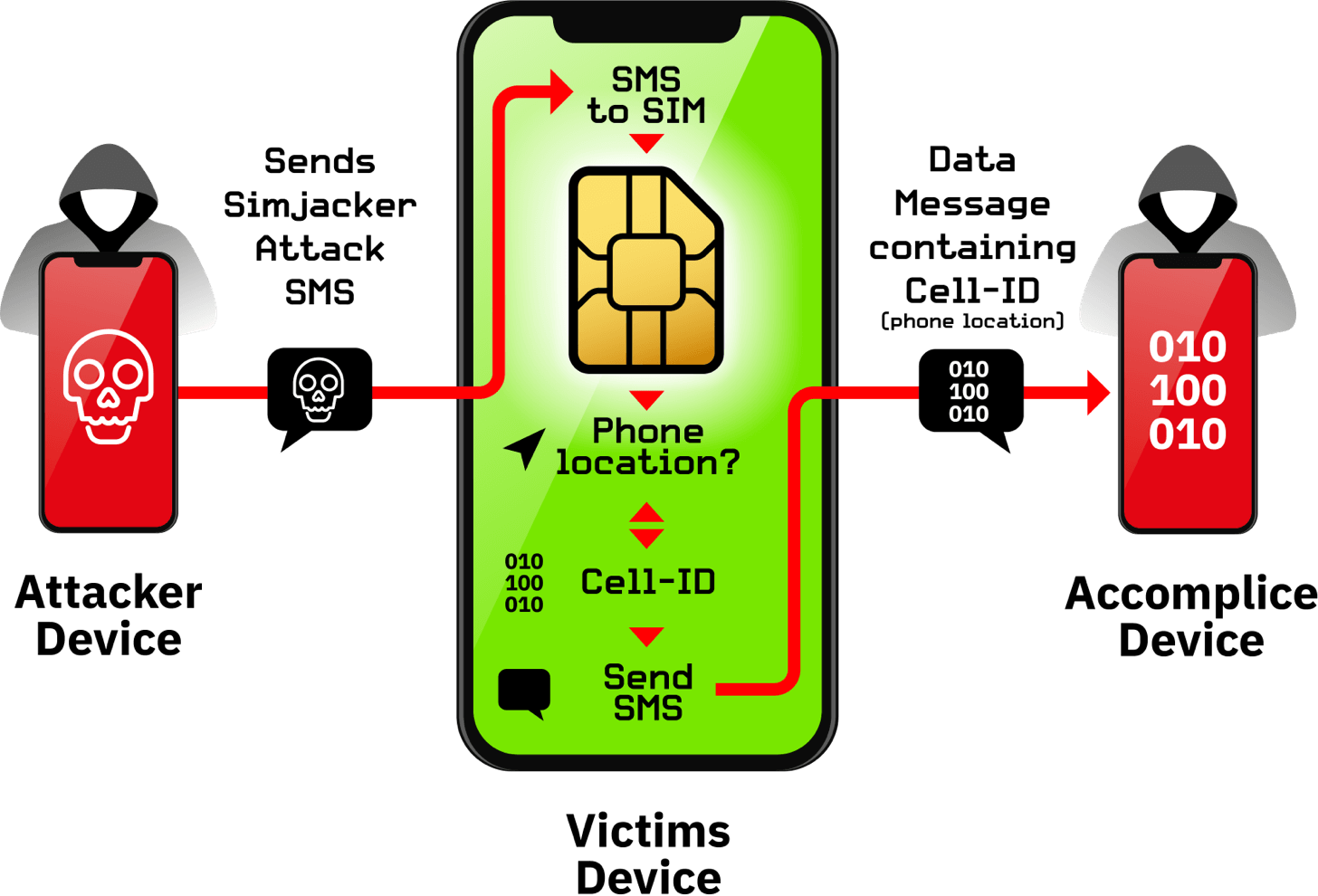
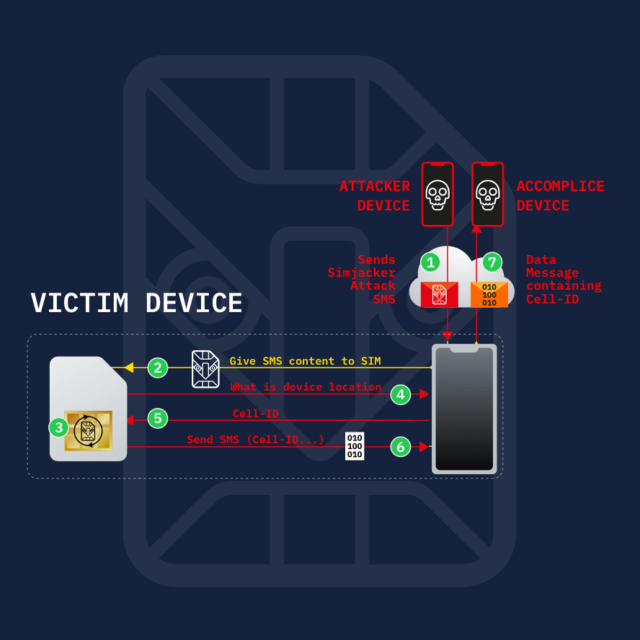
The main Simjacker attack involves an SMS containing a specific type of spyware-like code being sent to a mobile phone, which then instructs the SIM Card within the phone to ‘take over’ the mobile phone to retrieve and perform sensitive commands.
The location information of thousands of devices was obtained over time without the knowledge or consent of the targeted mobile phone users.
During the attack, the user is completely unaware that they received the attack, that information was retrieved, and that it was successfully exfiltrated.
The Simjacker attack can, and has been extended further to perform additional types of attacks.
Example of how Simjacker can track mobile phone location of vulnerable subscribers
The Scale of the Simjacker Vulnerability and Attacks
Simjacker has been further exploited to perform many other types of attacks against individuals and mobile operators such as fraud, scam calls, information leakage, denial of service and espionage. AdaptiveMobile Security Threat Intelligence analysts observed the hackers vary their attacks, testing many of these further exploits. In theory, all makes and models of mobile phone are open to attack as the vulnerability is linked to a technology embedded on SIM cards. The Simjacker vulnerability could extend to over 1 billion mobile phone users globally, potentially impacting countries in the Americas, West Africa, Europe, Middle East and indeed any region of the world where this SIM card technology is in use.
Stopping the attacks and building long-term defences
We are quite confident that this exploit has been developed by a specific private company that works with governments to monitor individuals. AdaptiveMobile Security has been working closely with their customers and the wider industry; including both mobile network operators and SIM card manufacturers to protect mobile phone subscribers. We have blocked attacks and are committed to using our global threat intelligence to build defences against these new sophisticated attacks that are circumventing current security measures.
Simjacker – Next Generation Spying Over Mobile
We believe that the Simjacker vulnerability has been exploited for at least the last 2 years by a highly sophisticated threat actor in multiple countries, primarily for the purposes of surveillance. Read on to discover more about this ground-breaking attack.
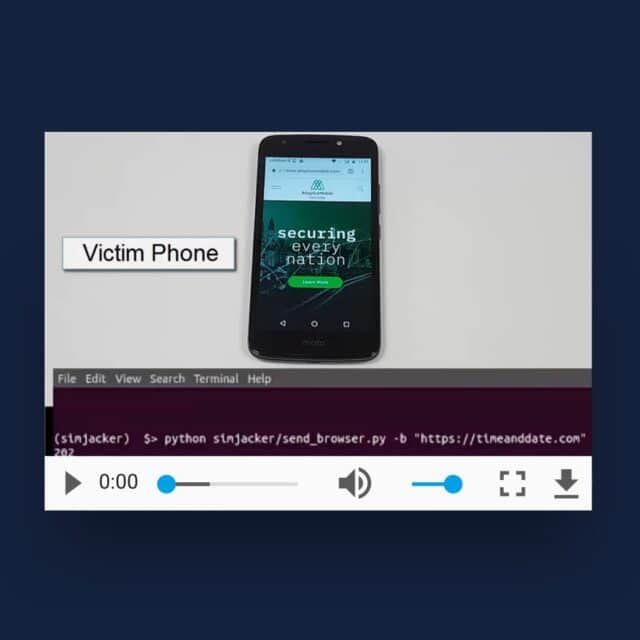
Simjacker – Frequently Asked Questions and Demos
Here we put the most common questions, as well as showing example demos of the Location retrieval and Browser-Opening attacks, made possible by Simjacker.
Protecting Mobile Network Operators
Enea is the world leader in mobile network security, protecting more than 2.2 billion subscribers worldwide. With deep expertise and a unique focus on network-to-handset security, Enea’s award-winning security solutions and services provide its customers with advanced threat detection and actionable intelligence, combined with the most comprehensive security product-set in the market today.
Enea counts some of the world’s largest carriers, CPaaS providers, governments, and regulators as customers.